- 06 April 2021
- Announcements
- 24 Comments
The Implications of Information Asymmetry and Disclosures for Security Tokens

In the crypto community, security tokens are a hot topic of discussion right now. Part of that dialogue involves what needs to be developed as the next era of security tokens arises. When looking at the ream of requirements for the second phase of security tokens, it’s no surprise to find disclosures headlining the list.
The subject of information disclosures is well worth delving into. Depending on who you ask, the absence of information disclosures has the potential to derail the successful development of crypto-securities in the future. The proper implementation of security token disclosures within a decentralised ecosystem is a paramount concern.
The risk factors associated with information asymmetry
Some might stress the importance of regulation and transparency in regards to information disclosures as they apply to security tokens, but the implications are far deeper than this. In fact, the importance of information tokens goes right to the very heart of market dynamics. Think about it in these simple terms: without access to information relevant to crypto-security, it’s impossible to ascertain whether we’re paying a reasonable price for it.
In the case of utility tokens, price is determined by trading market momentum and core token mechanics. However, these things have minimal relevance to crypto-securities. When it comes to security tokens, market behaviour is more more heavily associated with information about the tokenised asset itself. In the event of unreliable or threadbare information, inefficiencies in the market can be expected. This is often referred to as ‘Information Asymmetry’ by economists. Economists will also argue that information asymmetry is one of the chief risk factors working against the successful evolution of security tokens going forward.
The Modigliani-Miller theorem
Information asymmetry has been a staple concept of market economics since the 1970s. The concept of asymmetric information can be used to refer to a situation where one party involved in a trade his privy to certain information that other parties involved in the same trade are not. Detailed study into information asymmetry in regards to financial markets has delivered incredibly useful economic insights. One such contribution is the Modigliani-Miller theorem. This theorem outlines that the market value and financial structure of a company are in fact, not related. Rather, the market value is instead related to its apparent earning power and associated risks. Based upon this argument, the message is that information disclosures and potential incentives between shareholders and employees are more relevant and important than conventional financial models of a given asset.
The Market for Lemons — making sense of information asymmetric markets
One of the leading authorities in information asymmetric markets is Geroge Akerlof, a Nobel prize-winning American economist. Akerlof approached the subject of information asymmetry with his 1970 paper, “The Market for Lemons”, outlining the topic with real world examples. In his paper, Akerlof uses the example of a seller who holds information about the quality of a used auto-mobile. In this example, a buyer is keen to purchase a car, but is also keen on ensuring they pay a fair price for it. In the example, there are multiple available cars, with each one having a so-called fair value. These values are varied, however. In the event that the buyer cannot ascertain quality of each car, those sellers looking to offload a vehicle of lower quality will always ascertain they are selling one of higher quality at the highest potential asking price. The fair price will then reflect the average quality of the market. However, in this instance, those sellers with vehicles genuinely worth more than the decided market average will consider the average asking price, or fair value, too low. At this point, those sellers will exit the market. As a result of this market exiting, the average price drops further. Again, those sellers who have vehicles of a higher value than the new average will be encouraged to leave the market. The end result is that with the exception of the lowest quality vehicles, no sellers remain who are willing to sell a vehicle that a buyer is prepared to buy.
This pattern of behaviour reveals a principle that can be applied to security tokens. It establishes a precedent that shows how information asymmetry can prevent ideal market behaviour and overall evolution of the market. Any market where asymmetric information remains an active element have the potential to be plagued by nefarious trading tactics and business behaviour, whether that means insider trading or market manipulation. The end result is the same. A small fraction of the overall population engaged in the market who have access to information will benefit to the detriment of the majority. Disclosures, along with other things like liquidity protocols and pools, stand as one of the main influential factors on price in regards to crypto-securities.
Potential mechanisms for collection and analysis of information
Thorough guidelines relating to disclosures of public securities have been established by jurisdictions, including the United States. The Securities and Exchange Commission (SEC) not only outlined clear guidelines in respect of disclosures, but also unveiled the Electronic Data Gathering, Analysis and Retrieval System (EDGAR) in 1984. EDGAR was established as the chief mechanism for the collection and searching of information that might be relevant to public securities investment. This mechanism is utilised in several ways, but one key duty is to ensure those participating in the market engage so honestly. While it may operate in a centralised manner, a mechanism like EDGAR gives us thought on how to approach the notion of disclosures as they apply to security tokens and the crypto sector. In short, we need to consider implementing a decentralised version of EDGAR.
As it stands with the security tokens market today, disclosures are processed by so-called token insurance platforms in a centralised way. Such a model might suit the current era of the market, but there some significant risks associated with it and limitations which will hamper future development. This decentralised model means that market participants have to trust insurance platforms when it comes to validating information from issuers of tokens. Carrying out such checks on validity is almost impossible any any significant volume. Allowing for issuance platforms or exchanges to act as handler of disclosure information when it applies to security tokens causes considerable problems when we think about information asymmetry. However, security tokens present the opportunity to rethink the whole notion of disclosures going forward, particularly in regards to modern securities. A key consideration here is the idea of programmability.
Programmable protocols
When thinking about the introduction of a new protocol, it’s worth considering the three different parties that will interact with disclosures of a security token. Firstly, there’s the issuers of the token itself, or those who publish information relating to crypto-securities. Second, there’s the consumer. Consumers represent the token holders, token exchanges, or any other market participant making a decision relating to crypto-securities with disclosed information as an influence. Finally, you have the validators. These are market participants who have the role of can ascertain as to whether disclosed information holds up to scrutiny and is reflective of reality.
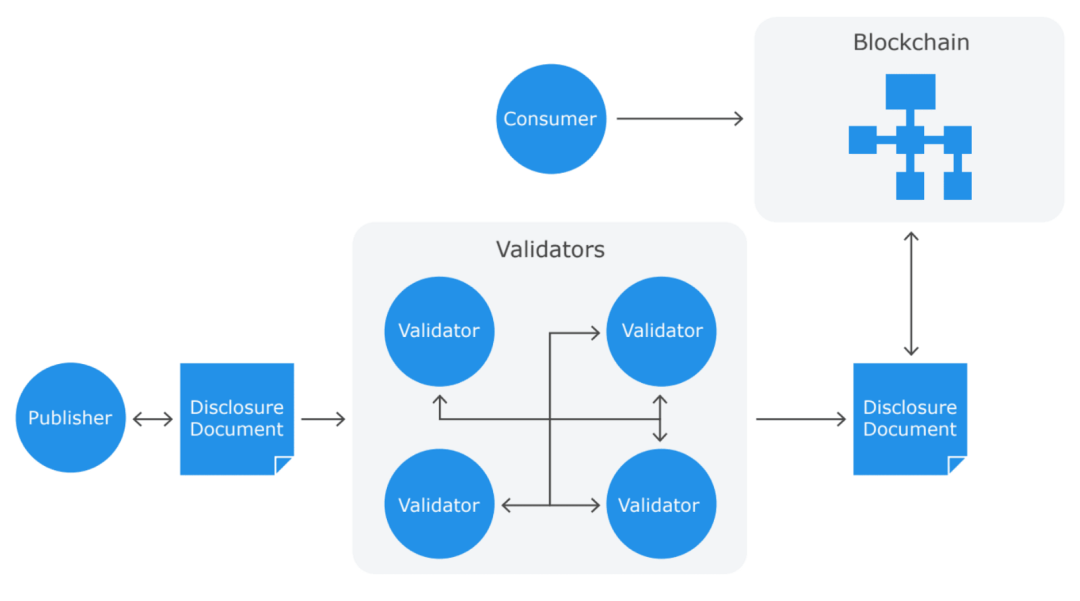
Taking into account these three distinct roles, we can consider the founding architecture of a future disclosure protocol specific to security tokens. Smart contracts of security tokens will not only include the essential mechanisms for publishing of tokens, but also for the validation of disclosure material. Various entities can serve as validators of disclosure information, be it an exchange or a token issuance platform. Encouraging interactions in this regard with token incentives is also worth considering.
Where next for security token disclosures?
When it comes to the security token market, the importance of disclosures can’t be ignored. They’re crucial in ensuring the market is seen as a legitimate one to investors, particularly larger entities. Admittedly, current models may need to be challenged in order to give disclosures the due attention and development needed, but left-field thinking may be the only way to carve a better future for this foundation concern.